iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
iGPT transforms email data into actionable insights through a secure API, enabling smarter enterprise workflows.
Last updated: March 1, 2026
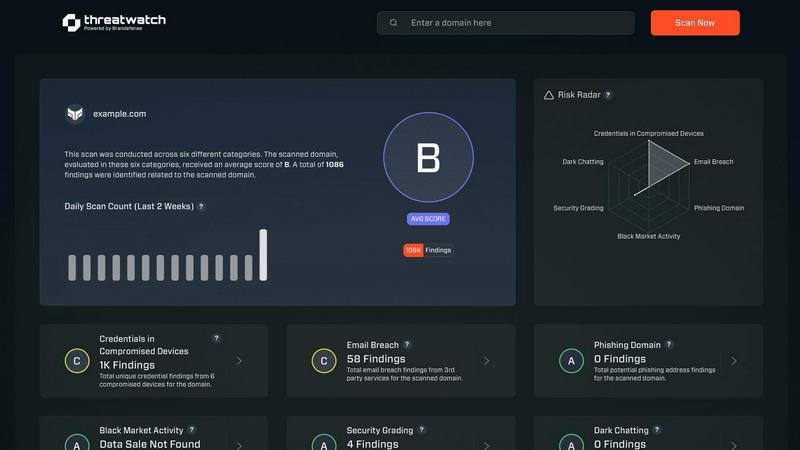
Threat Watch
Elevate your cybersecurity with Threat Watch, delivering rapid assessments and actionable insights to safeguard your.
Last updated: March 1, 2026
Visual Comparison
iGPT

Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT offers an SDK and a live playground that allows users to quickly test requests and responses. This immediate integration capability ensures that enterprises can start harnessing the power of email intelligence without lengthy setup processes.
Contextual Responses
The API provides responses that are ready for reasoning and automation, complete with citations to the source materials. This feature enhances the reliability of the information retrieved and allows businesses to maintain accuracy in their operational decisions.
Hybrid Retrieval
iGPT employs a sophisticated hybrid retrieval system that combines semantic and keyword searches with filters. This ensures that users receive the most relevant information in one seamless call, optimizing the efficiency of data retrieval from extensive email archives.
Continuous Data Indexing
With real-time ingestion capabilities, iGPT continuously indexes new messages and attachments. This ensures that the data and answers remain up-to-date, providing organizations with the most current insights available.
Threat Watch
Comprehensive Security Assessment
Threat Watch evaluates critical security categories, providing a holistic view of your cyber health. This includes assessments of compromised credentials, breached accounts, phishing addresses, and dark web content, ensuring no vulnerability goes unnoticed.
Real-time Threat Intelligence
With its continuous monitoring capabilities, Threat Watch delivers real-time updates on your organization's security landscape. This feature ensures that security teams have immediate access to the latest threat intelligence, enabling swift and informed decision-making.
Actionable Risk Scoring
The platform's ability to crystallize your cyber health into a clear, comprehensible score empowers organizations to prioritize risks effectively. This scoring system allows teams to focus on the most pressing vulnerabilities, facilitating efficient resource allocation for risk mitigation.
Automated Vulnerability Assessments
Threat Watch automates the assessment process, significantly reducing the time and effort required to evaluate security postures. This feature streamlines workflows and enhances operational efficiency, allowing teams to concentrate on strategic initiatives rather than manual assessments.
Use Cases
iGPT
Email Assistants
Organizations can build intelligent agents using iGPT that can draft, prioritize, and act on emails with complete context. This capability streamlines communication processes and enhances overall productivity.
Workflow Automation
iGPT enables businesses to convert email threads into actionable tasks, deadlines, and approvals. By flagging items that are stuck, organizations can ensure smoother workflow progression and accountability.
Support Copilots
The API can reconstruct the full customer story across lengthy email chains, attachments, and varying tones. This assists support teams in understanding customer contexts, leading to improved service delivery.
CRM Agents
iGPT extracts crucial decisions, owners, and deal momentum directly from email threads. This functionality allows sales teams to leverage insights from communication data to drive engagement and close deals effectively.
Threat Watch
Executive Security Oversight
CISOs and executive leadership can utilize Threat Watch to gain a comprehensive understanding of their organization’s cybersecurity health. The platform's actionable insights enable informed discussions at the executive level regarding risk management and resource allocation.
Incident Response Optimization
Security teams can leverage Threat Watch during incident response scenarios to quickly identify vulnerabilities and prioritize remediation efforts. The real-time threat intelligence enables a rapid and focused response to emerging threats.
Compliance and Regulatory Reporting
Organizations can use Threat Watch to generate reports that demonstrate compliance with various regulatory requirements. The platform’s detailed assessments and scoring provide essential documentation for audits and compliance checks.
Proactive Risk Management
Threat Watch empowers organizations to adopt a proactive approach to cybersecurity by continuously monitoring for potential vulnerabilities. This forward-thinking strategy helps mitigate risks before they can be exploited, enhancing overall organizational resilience.
Overview
About iGPT
iGPT is an advanced email intelligence API that leverages state-of-the-art AI technology to transform email conversations and attachments into actionable insights. Designed for enterprises, iGPT empowers organizations to harness the power of their communication data, facilitating better decision-making and enhanced workflows. By providing a secure and auditable gateway, iGPT ensures that businesses can access, comprehend, and utilize their email data effectively while maintaining compliance. The product features a unified infrastructure with granular access controls and comprehensive audit trails, allowing enterprises to deploy AI agents confidently. With iGPT, organizations can extract trusted, context-aware answers from their email data, driving productivity and operational excellence. This makes iGPT an indispensable tool for businesses seeking to optimize their email communication and leverage it for strategic advantage.
About Threat Watch
Threat Watch is the premier cybersecurity intelligence platform designed for elite organizations that refuse to accept the status quo of digital insecurity. It goes beyond mere monitoring, providing a cohesive, real-time overview of your cybersecurity posture. Tailored for Chief Information Security Officers (CISOs), security teams, and executive leadership, Threat Watch delivers not only raw data but also actionable, prioritized intelligence that can inform strategic decisions. By meticulously analyzing your entire asset landscape, identifying external vulnerabilities, and monitoring deep-web exposures, Threat Watch translates complex cyber health metrics into a straightforward, comprehensible score. Its core value proposition lies in transforming an overwhelming influx of threat data into a strategic roadmap, which enables organizations to pinpoint critical risks, automate assessments, and execute mitigation strategies with unparalleled speed and precision. This platform serves as the command center for proactive defense, empowering enterprises to stay not just reactive but resiliently ahead of emerging threats.
Frequently Asked Questions
iGPT FAQ
What kind of data does iGPT process?
iGPT processes email conversations and attachments, providing contextual insights while ensuring that sensitive information remains secure and compliant.
How does iGPT ensure data security?
iGPT employs zero data retention policies, role-based access control, and OAuth-only processing to protect sensitive information and maintain enterprise-grade security at every level.
Can iGPT integrate with existing systems?
Yes, iGPT is designed for seamless integration within existing enterprise systems, allowing organizations to enhance their workflows without overhauling their current processes.
What types of organizations benefit from iGPT?
iGPT is tailored for enterprises across various sectors looking to leverage email intelligence to enhance decision-making, optimize workflows, and drive operational excellence.
Threat Watch FAQ
How does Threat Watch evaluate my organization's cybersecurity health?
Threat Watch utilizes a comprehensive assessment of various security categories, including compromised credentials and breached accounts, to provide a clear and actionable score reflecting your cyber health.
Is Threat Watch suitable for small businesses?
While Threat Watch is designed for elite organizations, its scalable features can be beneficial for businesses of all sizes, especially those looking to enhance their cybersecurity posture and risk management strategies.
How often is the threat intelligence updated?
Threat Watch provides real-time updates, ensuring that your organization receives the most current threat intelligence available, allowing for timely responses to emerging security risks.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your overall cybersecurity framework without disrupting current operations.
Alternatives
iGPT Alternatives
iGPT is a sophisticated email intelligence API that empowers enterprises to transform their vast email data into actionable insights. Positioned within the realm of business intelligence, it leverages advanced AI technology to provide a secure and auditable gateway for organizations to enhance their communication data utilization. Users often seek alternatives to iGPT due to various factors such as pricing structures, feature sets, or specific platform requirements that may better align with their unique business needs. When choosing an alternative, it is essential to consider factors such as ease of integration, the reliability of insights, scalability, and security measures. Organizations should also evaluate the context-aware capabilities of the alternative solutions to ensure they can extract meaningful, actionable insights from their email communications, thus driving productivity and operational excellence.
Threat Watch Alternatives
Threat Watch is a premier cybersecurity intelligence platform designed for elite organizations seeking to enhance their digital security posture. As a leader in the business intelligence category, it offers a comprehensive view of your cybersecurity landscape, empowering executives and security teams with actionable insights. Users often seek alternatives due to various reasons, including pricing structures, feature sets, and specific platform requirements that may better align with their unique security needs. When exploring alternatives, it is essential to consider the depth of intelligence provided, the user experience of the dashboard, real-time monitoring capabilities, and the extent of automated assessments to ensure a robust cybersecurity strategy.
