Threat Watch
Elevate your cybersecurity with Threat Watch, delivering rapid assessments and actionable insights to safeguard your.
Visit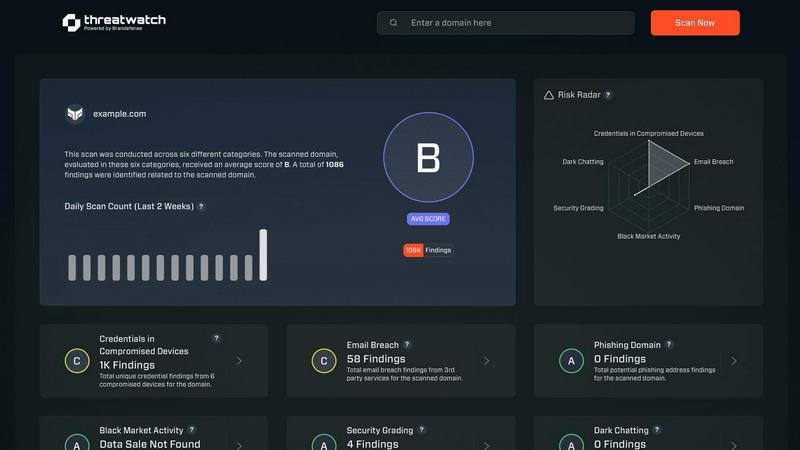
About Threat Watch
Threat Watch is the premier cybersecurity intelligence platform designed for elite organizations that refuse to accept the status quo of digital insecurity. It goes beyond mere monitoring, providing a cohesive, real-time overview of your cybersecurity posture. Tailored for Chief Information Security Officers (CISOs), security teams, and executive leadership, Threat Watch delivers not only raw data but also actionable, prioritized intelligence that can inform strategic decisions. By meticulously analyzing your entire asset landscape, identifying external vulnerabilities, and monitoring deep-web exposures, Threat Watch translates complex cyber health metrics into a straightforward, comprehensible score. Its core value proposition lies in transforming an overwhelming influx of threat data into a strategic roadmap, which enables organizations to pinpoint critical risks, automate assessments, and execute mitigation strategies with unparalleled speed and precision. This platform serves as the command center for proactive defense, empowering enterprises to stay not just reactive but resiliently ahead of emerging threats.
Features of Threat Watch
Comprehensive Security Assessment
Threat Watch evaluates critical security categories, providing a holistic view of your cyber health. This includes assessments of compromised credentials, breached accounts, phishing addresses, and dark web content, ensuring no vulnerability goes unnoticed.
Real-time Threat Intelligence
With its continuous monitoring capabilities, Threat Watch delivers real-time updates on your organization's security landscape. This feature ensures that security teams have immediate access to the latest threat intelligence, enabling swift and informed decision-making.
Actionable Risk Scoring
The platform's ability to crystallize your cyber health into a clear, comprehensible score empowers organizations to prioritize risks effectively. This scoring system allows teams to focus on the most pressing vulnerabilities, facilitating efficient resource allocation for risk mitigation.
Automated Vulnerability Assessments
Threat Watch automates the assessment process, significantly reducing the time and effort required to evaluate security postures. This feature streamlines workflows and enhances operational efficiency, allowing teams to concentrate on strategic initiatives rather than manual assessments.
Use Cases of Threat Watch
Executive Security Oversight
CISOs and executive leadership can utilize Threat Watch to gain a comprehensive understanding of their organization’s cybersecurity health. The platform's actionable insights enable informed discussions at the executive level regarding risk management and resource allocation.
Incident Response Optimization
Security teams can leverage Threat Watch during incident response scenarios to quickly identify vulnerabilities and prioritize remediation efforts. The real-time threat intelligence enables a rapid and focused response to emerging threats.
Compliance and Regulatory Reporting
Organizations can use Threat Watch to generate reports that demonstrate compliance with various regulatory requirements. The platform’s detailed assessments and scoring provide essential documentation for audits and compliance checks.
Proactive Risk Management
Threat Watch empowers organizations to adopt a proactive approach to cybersecurity by continuously monitoring for potential vulnerabilities. This forward-thinking strategy helps mitigate risks before they can be exploited, enhancing overall organizational resilience.
Frequently Asked Questions
How does Threat Watch evaluate my organization's cybersecurity health?
Threat Watch utilizes a comprehensive assessment of various security categories, including compromised credentials and breached accounts, to provide a clear and actionable score reflecting your cyber health.
Is Threat Watch suitable for small businesses?
While Threat Watch is designed for elite organizations, its scalable features can be beneficial for businesses of all sizes, especially those looking to enhance their cybersecurity posture and risk management strategies.
How often is the threat intelligence updated?
Threat Watch provides real-time updates, ensuring that your organization receives the most current threat intelligence available, allowing for timely responses to emerging security risks.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your overall cybersecurity framework without disrupting current operations.
Explore more in this category:
Similar to Threat Watch
AI Business Name Generator
Elevate your brand with our AI Business Name Generator, delivering unique and memorable names tailored for startups and innovative ventures.
BTAQA DIGITAL LOYALTY CARDS
BTAQA Digital Loyalty Cards transform customer engagement by rewarding loyalty and providing actionable insights to boost retention.
Opal44
Opal44 transforms your GA4 data into clear, actionable insights, making website analytics effortlessly understandable.
Fusedash
Fusedash transforms raw data into intuitive dashboards and charts, enabling teams to act on insights with precision.
finban
finban empowers confident decision-making with real-time liquidity planning, streamlining forecasts and budgets.
aVenture
aVenture empowers investors with institutional-grade insights to analyze and track over 100,000 private companies.
iGPT
iGPT transforms email data into actionable insights through a secure API, enabling smarter enterprise workflows.
Karolium
Karolium is the elite zero-code platform that accelerates digital transformation with AI-driven business solutions.