Deeploy vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Deeploy
Deeploy provides elite governance infrastructure for secure, compliant AI scaling.
Last updated: March 1, 2026
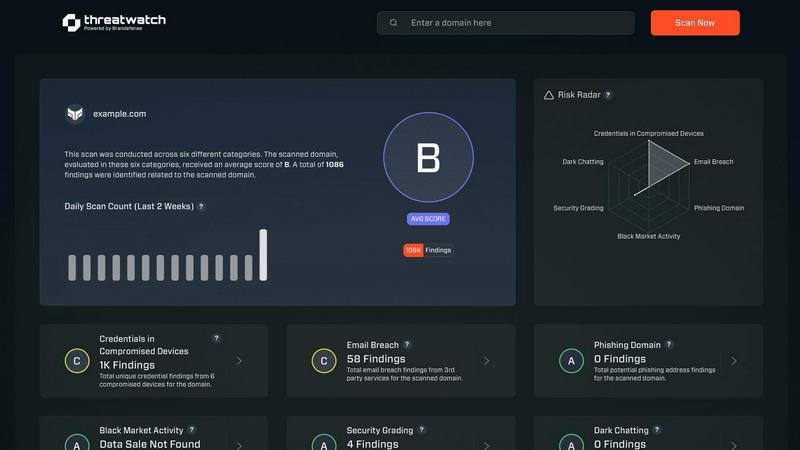
Threat Watch
Elevate your cybersecurity with Threat Watch, delivering rapid assessments and actionable insights to safeguard your.
Last updated: March 1, 2026
Visual Comparison
Deeploy
Threat Watch
Feature Comparison
Deeploy
AI Discovery and Onboarding
Deeploy provides complete visibility across your entire AI landscape, eliminating dangerous blind spots. From a single, intuitive interface, you can discover, onboard, and manage every AI system—whether built in-house, sourced from third-party vendors, or embedded in other software. The platform connects seamlessly to any MLOps or GenAI platform, establishing centralized control without the need for costly and complex migration projects, ensuring no AI initiative operates in the shadows.
Control Frameworks
Navigate the complex web of global AI regulations with confidence using Deeploy's structured control frameworks. The platform offers default frameworks aligned with major standards like ISO 42001 and the NIST AI RMF, or allows you to build custom ones tailored to internal policies. This feature enables you to classify AI system risk levels in minutes and establish clear accountability through defined approval processes, turning regulatory complexity into a straightforward, manageable workflow.
Control Implementation
Deeploy translates high-level governance policies into clear, actionable requirements that engineers will actually follow. It automates the governance process by applying the correct controls to each AI system based on its risk classification. This accelerates compliance by up to 90% through the use of pre-built templates and the automatic collection of audit evidence, moving governance from a manual, bureaucratic hurdle to an integrated, efficient part of the development lifecycle.
Real-Time Monitoring
Proactively prevent AI incidents and compliance breaches with Deeploy's continuous monitoring capabilities. The system provides instant alerts for critical issues like model drift, performance degradation, and output anomalies, allowing you to intervene before users are impacted. For LLMs, it adds essential tracing and guardrails to protect outputs. This real-time oversight ensures AI systems perform as intended and remain within defined ethical and operational boundaries.
Threat Watch
Comprehensive Security Assessment
Threat Watch evaluates critical security categories, providing a holistic view of your cyber health. This includes assessments of compromised credentials, breached accounts, phishing addresses, and dark web content, ensuring no vulnerability goes unnoticed.
Real-time Threat Intelligence
With its continuous monitoring capabilities, Threat Watch delivers real-time updates on your organization's security landscape. This feature ensures that security teams have immediate access to the latest threat intelligence, enabling swift and informed decision-making.
Actionable Risk Scoring
The platform's ability to crystallize your cyber health into a clear, comprehensible score empowers organizations to prioritize risks effectively. This scoring system allows teams to focus on the most pressing vulnerabilities, facilitating efficient resource allocation for risk mitigation.
Automated Vulnerability Assessments
Threat Watch automates the assessment process, significantly reducing the time and effort required to evaluate security postures. This feature streamlines workflows and enhances operational efficiency, allowing teams to concentrate on strategic initiatives rather than manual assessments.
Use Cases
Deeploy
Enterprise-Wide AI Inventory and Compliance
For large organizations with AI scattered across departments, Deeploy solves the fundamental challenge of creating a single source of truth. It enables the discovery and documentation of all AI assets into a centralized registry. This is the critical first step for complying with regulations like the EU AI Act, providing auditors and executives with a complete, up-to-date inventory and demonstrating organized oversight of all AI initiatives.
Accelerating AI Deployment with Governance
Deeploy is used by AI teams to drastically reduce the time from model development to governed production. By integrating governance checks directly into the deployment pipeline, it ensures new models meet all compliance requirements from day one. This turns a process that traditionally took days or weeks into one that can be completed in hours, allowing organizations to scale AI faster without sacrificing control or creating future technical debt.
Proactive Risk Mitigation in High-Stakes Industries
In sectors like healthcare, finance, and critical infrastructure, Deeploy provides the essential safety net for AI systems. Its real-time monitoring and explainability features allow organizations to continuously validate AI decisions, detect drift in predictive models, and implement human-in-the-loop feedback mechanisms. This enables the safe and responsible application of AI where errors could have severe consequences, building necessary trust with users and regulators.
Streamlining Audit and Evidence Collection
Deeploy automates the most burdensome aspect of AI governance: audit preparation. It automatically collects and documents evidence that controls are functioning as designed. When an audit occurs, compliance teams can generate comprehensive reports with a few clicks, proving due diligence and adherence to frameworks without manual, error-prone evidence gathering, saving hundreds of hours and ensuring audit readiness at all times.
Threat Watch
Executive Security Oversight
CISOs and executive leadership can utilize Threat Watch to gain a comprehensive understanding of their organization’s cybersecurity health. The platform's actionable insights enable informed discussions at the executive level regarding risk management and resource allocation.
Incident Response Optimization
Security teams can leverage Threat Watch during incident response scenarios to quickly identify vulnerabilities and prioritize remediation efforts. The real-time threat intelligence enables a rapid and focused response to emerging threats.
Compliance and Regulatory Reporting
Organizations can use Threat Watch to generate reports that demonstrate compliance with various regulatory requirements. The platform’s detailed assessments and scoring provide essential documentation for audits and compliance checks.
Proactive Risk Management
Threat Watch empowers organizations to adopt a proactive approach to cybersecurity by continuously monitoring for potential vulnerabilities. This forward-thinking strategy helps mitigate risks before they can be exploited, enhancing overall organizational resilience.
Overview
About Deeploy
Deeploy is the definitive AI Governance platform for elite enterprises that refuse to compromise between innovation and integrity. In a landscape where AI systems are proliferating across models, vendors, and embedded applications, Deeploy provides the critical infrastructure for complete oversight. It is engineered for organizations running AI at scale who face stringent regulatory pressures, such as the EU AI Act, and demand absolute control over their AI ecosystem. The platform transforms a fragmented and risky AI landscape into a governed, compliant, and transparent portfolio. By offering a centralized registry, real-time monitoring, and enforceable control frameworks, Deeploy empowers risk, compliance, and technology leaders to scale AI initiatives with unprecedented speed and confidence. Its core value proposition is singular: enabling businesses to harness the transformative power of AI while systematically eliminating operational, reputational, and compliance risks, thereby fostering essential trust with stakeholders and regulators.
About Threat Watch
Threat Watch is the premier cybersecurity intelligence platform designed for elite organizations that refuse to accept the status quo of digital insecurity. It goes beyond mere monitoring, providing a cohesive, real-time overview of your cybersecurity posture. Tailored for Chief Information Security Officers (CISOs), security teams, and executive leadership, Threat Watch delivers not only raw data but also actionable, prioritized intelligence that can inform strategic decisions. By meticulously analyzing your entire asset landscape, identifying external vulnerabilities, and monitoring deep-web exposures, Threat Watch translates complex cyber health metrics into a straightforward, comprehensible score. Its core value proposition lies in transforming an overwhelming influx of threat data into a strategic roadmap, which enables organizations to pinpoint critical risks, automate assessments, and execute mitigation strategies with unparalleled speed and precision. This platform serves as the command center for proactive defense, empowering enterprises to stay not just reactive but resiliently ahead of emerging threats.
Frequently Asked Questions
Deeploy FAQ
How does Deeploy handle AI systems from different vendors and platforms?
Deeploy is designed as a unifying governance layer that sits above your existing AI stack. It offers flexible connectors and APIs to integrate with any major MLOps platform, cloud AI service, or custom-built system. This means you can gain centralized oversight and apply consistent governance policies across all your AI investments without needing to rip and replace your current technologies, eliminating blind spots and migration pain.
Can Deeploy help us comply with the EU AI Act specifically?
Absolutely. Deeploy is built with regulations like the EU AI Act as a primary focus. Its control frameworks include pre-mapped requirements for high-risk AI system obligations. The platform guides you through risk classification, documentation creation, transparency measures, and human oversight implementation—all core tenets of the Act. Automated evidence collection directly supports the creation of the required technical documentation for compliance demonstrations.
Is Deeploy suitable for governing Generative AI and LLMs?
Yes, Deeploy provides specific governance capabilities for Generative AI. Beyond standard model monitoring, it includes features for tracing LLM outputs, implementing guardrails to prevent harmful or non-compliant content, and assessing the risk of generative applications. This ensures that even the most complex and novel AI systems are brought under the same umbrella of responsible oversight and control.
How does Deeploy ensure that governance policies are adopted by technical teams?
Deeploy bridges the gap between policy and practice by translating governance frameworks into clear, engineer-friendly requirements within their existing workflows. It integrates with development tools and provides actionable tasks, not just documentation. By automating evidence collection and using templates, it removes manual burden, making compliance the path of least resistance and ensuring high adoption rates across technical teams.
Threat Watch FAQ
How does Threat Watch evaluate my organization's cybersecurity health?
Threat Watch utilizes a comprehensive assessment of various security categories, including compromised credentials and breached accounts, to provide a clear and actionable score reflecting your cyber health.
Is Threat Watch suitable for small businesses?
While Threat Watch is designed for elite organizations, its scalable features can be beneficial for businesses of all sizes, especially those looking to enhance their cybersecurity posture and risk management strategies.
How often is the threat intelligence updated?
Threat Watch provides real-time updates, ensuring that your organization receives the most current threat intelligence available, allowing for timely responses to emerging security risks.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your overall cybersecurity framework without disrupting current operations.
Alternatives
Deeploy Alternatives
Deeploy is an elite AI Governance platform within the Business Intelligence category, designed to provide organizations with complete oversight, compliance, and risk management for their AI ecosystems. It is the definitive solution for enterprises that require rigorous control and real-time monitoring to meet stringent regulatory standards. Organizations may explore alternatives to Deeploy for various strategic reasons. These can include specific budgetary considerations, the need for different feature integrations, or platform requirements that align with a unique technological stack. The search for a different solution is a natural part of selecting the precise governance tools to match an enterprise's scale and complexity. When evaluating an alternative, discerning leaders prioritize a platform's ability to deliver comprehensive AI lifecycle governance, robust compliance automation, and real-time explainability. The ideal solution should offer seamless onboarding, enforceable control frameworks, and continuous monitoring to mitigate risk and build institutional trust, without compromising on enterprise-grade security and scalability.
Threat Watch Alternatives
Threat Watch is a premier cybersecurity intelligence platform designed for elite organizations seeking to enhance their digital security posture. As a leader in the business intelligence category, it offers a comprehensive view of your cybersecurity landscape, empowering executives and security teams with actionable insights. Users often seek alternatives due to various reasons, including pricing structures, feature sets, and specific platform requirements that may better align with their unique security needs. When exploring alternatives, it is essential to consider the depth of intelligence provided, the user experience of the dashboard, real-time monitoring capabilities, and the extent of automated assessments to ensure a robust cybersecurity strategy.
