AutoPhish vs Threat Watch
Side-by-side comparison to help you choose the right tool.
AutoPhish enhances organizational security with AI-driven phishing simulations and tailored training for a vigilant.
Last updated: March 1, 2026
Threat Watch
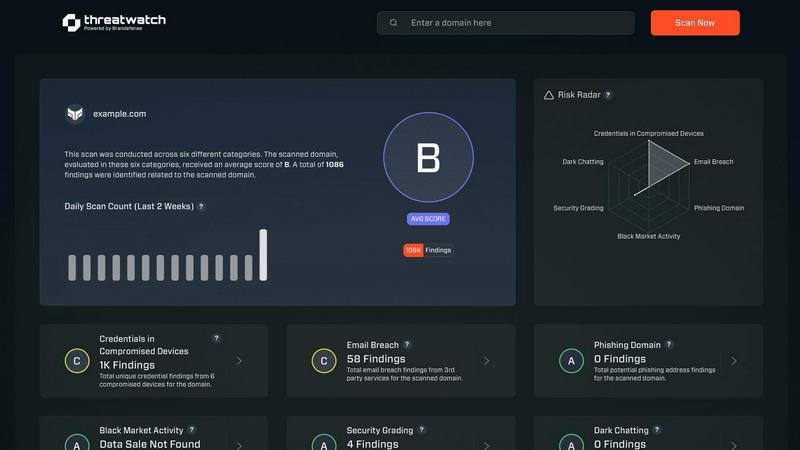
Elevate your cybersecurity with Threat Watch, delivering rapid assessments and actionable insights to safeguard your.
Last updated: March 1, 2026
Visual Comparison
AutoPhish

Threat Watch
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish employs sophisticated AI algorithms to craft phishing emails that authentically replicate real-world attacks, ensuring that training scenarios are both relevant and engaging for employees. This realistic approach not only boosts awareness but also enhances the retention of critical security practices.
Automated Campaigns
With AutoPhish, organizations can effortlessly schedule and execute phishing simulations automatically. This feature not only saves valuable administrative time but also guarantees that training remains consistent and systematic, allowing teams to focus on enhancing their security posture.
Targeted Training
AutoPhish offers a unique capability to assign specific security awareness training based on the results of phishing simulations and the roles of individual users. This targeted approach ensures that employees receive the most relevant training, addressing their unique vulnerabilities and reinforcing essential security practices.
Comprehensive Analytics
The platform provides in-depth analytics and reporting features that allow organizations to monitor simulation outcomes and identify vulnerable users. This data-driven insight empowers companies to implement effective follow-up training, significantly improving overall cybersecurity awareness and resilience.
Threat Watch
Comprehensive Security Assessment
Threat Watch evaluates critical security categories, providing a holistic view of your cyber health. This includes assessments of compromised credentials, breached accounts, phishing addresses, and dark web content, ensuring no vulnerability goes unnoticed.
Real-time Threat Intelligence
With its continuous monitoring capabilities, Threat Watch delivers real-time updates on your organization's security landscape. This feature ensures that security teams have immediate access to the latest threat intelligence, enabling swift and informed decision-making.
Actionable Risk Scoring
The platform's ability to crystallize your cyber health into a clear, comprehensible score empowers organizations to prioritize risks effectively. This scoring system allows teams to focus on the most pressing vulnerabilities, facilitating efficient resource allocation for risk mitigation.
Automated Vulnerability Assessments
Threat Watch automates the assessment process, significantly reducing the time and effort required to evaluate security postures. This feature streamlines workflows and enhances operational efficiency, allowing teams to concentrate on strategic initiatives rather than manual assessments.
Use Cases
AutoPhish
Employee Training Enhancement
Organizations can utilize AutoPhish to enhance their employee training programs by incorporating realistic phishing simulations. This practical experience helps employees to recognize and respond appropriately to phishing attempts, thereby reducing the likelihood of successful attacks.
Vulnerability Assessment
AutoPhish serves as a powerful tool for conducting vulnerability assessments within teams. By simulating phishing attacks, organizations can pinpoint weaknesses in their security protocols and address them proactively, fortifying their defenses against potential threats.
Compliance and Risk Management
For businesses operating in regulated industries, AutoPhish aids in meeting compliance requirements related to cybersecurity training. By consistently conducting phishing simulations and providing tailored training, organizations can demonstrate their commitment to risk management and employee education.
Cybersecurity Culture Development
By integrating AutoPhish into their security strategy, organizations can foster a culture of cybersecurity awareness. This proactive approach engages employees at all levels, making them active participants in safeguarding the organization's digital assets and creating a more resilient workforce.
Threat Watch
Executive Security Oversight
CISOs and executive leadership can utilize Threat Watch to gain a comprehensive understanding of their organization’s cybersecurity health. The platform's actionable insights enable informed discussions at the executive level regarding risk management and resource allocation.
Incident Response Optimization
Security teams can leverage Threat Watch during incident response scenarios to quickly identify vulnerabilities and prioritize remediation efforts. The real-time threat intelligence enables a rapid and focused response to emerging threats.
Compliance and Regulatory Reporting
Organizations can use Threat Watch to generate reports that demonstrate compliance with various regulatory requirements. The platform’s detailed assessments and scoring provide essential documentation for audits and compliance checks.
Proactive Risk Management
Threat Watch empowers organizations to adopt a proactive approach to cybersecurity by continuously monitoring for potential vulnerabilities. This forward-thinking strategy helps mitigate risks before they can be exploited, enhancing overall organizational resilience.
Overview
About AutoPhish
AutoPhish is a premier AI-driven platform meticulously crafted to elevate organizational cybersecurity by delivering hyper-realistic phishing simulations and precision-targeted security awareness training. Tailored for businesses across diverse sectors, AutoPhish harnesses the power of advanced artificial intelligence to generate phishing emails that closely resemble actual threats, ensuring that training remains relevant and impactful. The platform's primary value proposition lies in its ability to proactively detect vulnerabilities within teams, equipping employees with the essential skills and knowledge needed to identify and mitigate potential attacks before they escalate into crises. With features such as automated campaign management and personalized training modules, AutoPhish simplifies the execution of phishing tests while tailoring educational content based on simulation outcomes and user roles. This strategic approach cultivates a robust culture of security awareness, empowering organizations to stay ahead of emerging threats and protect their vital assets.
About Threat Watch
Threat Watch is the premier cybersecurity intelligence platform designed for elite organizations that refuse to accept the status quo of digital insecurity. It goes beyond mere monitoring, providing a cohesive, real-time overview of your cybersecurity posture. Tailored for Chief Information Security Officers (CISOs), security teams, and executive leadership, Threat Watch delivers not only raw data but also actionable, prioritized intelligence that can inform strategic decisions. By meticulously analyzing your entire asset landscape, identifying external vulnerabilities, and monitoring deep-web exposures, Threat Watch translates complex cyber health metrics into a straightforward, comprehensible score. Its core value proposition lies in transforming an overwhelming influx of threat data into a strategic roadmap, which enables organizations to pinpoint critical risks, automate assessments, and execute mitigation strategies with unparalleled speed and precision. This platform serves as the command center for proactive defense, empowering enterprises to stay not just reactive but resiliently ahead of emerging threats.
Frequently Asked Questions
AutoPhish FAQ
What types of businesses can benefit from using AutoPhish?
AutoPhish is designed to cater to businesses across various industries, including finance, healthcare, education, and technology. Any organization seeking to enhance its cybersecurity posture and employee awareness can benefit from its features.
How does AutoPhish create realistic phishing simulations?
AutoPhish utilizes advanced AI technology to analyze current phishing tactics and trends, allowing it to generate simulations that closely mimic real-world phishing attacks tailored to specific industries and organizational contexts.
Is there a limit to the number of simulations I can run?
AutoPhish offers different pricing tiers that dictate the number of simulated emails you can send per month. Depending on your chosen plan, you can run anywhere from 25 to 500 simulated emails monthly.
How can I assess the effectiveness of the training provided by AutoPhish?
AutoPhish provides comprehensive analytics and reporting features that allow organizations to track the performance of their phishing simulations and the effectiveness of subsequent training. This data helps in determining areas for improvement and refining training approaches.
Threat Watch FAQ
How does Threat Watch evaluate my organization's cybersecurity health?
Threat Watch utilizes a comprehensive assessment of various security categories, including compromised credentials and breached accounts, to provide a clear and actionable score reflecting your cyber health.
Is Threat Watch suitable for small businesses?
While Threat Watch is designed for elite organizations, its scalable features can be beneficial for businesses of all sizes, especially those looking to enhance their cybersecurity posture and risk management strategies.
How often is the threat intelligence updated?
Threat Watch provides real-time updates, ensuring that your organization receives the most current threat intelligence available, allowing for timely responses to emerging security risks.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to seamlessly integrate with a variety of existing security tools and systems, enhancing your overall cybersecurity framework without disrupting current operations.
Alternatives
AutoPhish Alternatives
AutoPhish is an elite AI-driven platform that enhances cybersecurity for organizations through realistic phishing simulations and targeted training. It belongs to the Business Intelligence and Productivity & Management category, catering to diverse industries seeking to bolster their security posture. Users often seek alternatives due to various reasons such as pricing, specific feature sets, or compatibility with their existing platforms and workflows. When evaluating alternatives, it is crucial to consider the quality of simulations, the adaptability of training materials, the ease of use, and the level of customization available to tailor the experience to the organization's unique needs.
Threat Watch Alternatives
Threat Watch is a premier cybersecurity intelligence platform designed for elite organizations seeking to enhance their digital security posture. As a leader in the business intelligence category, it offers a comprehensive view of your cybersecurity landscape, empowering executives and security teams with actionable insights. Users often seek alternatives due to various reasons, including pricing structures, feature sets, and specific platform requirements that may better align with their unique security needs. When exploring alternatives, it is essential to consider the depth of intelligence provided, the user experience of the dashboard, real-time monitoring capabilities, and the extent of automated assessments to ensure a robust cybersecurity strategy.
