Hush Touch | Voice-to-Text for MacOS vs RedVeil
Side-by-side comparison to help you choose the right tool.
Hush Touch | Voice-to-Text for MacOS
Hush Touch delivers intelligent offline voice-to-text dictation for Mac, learning your vocabulary for flawless.
Last updated: February 28, 2026
RedVeil
RedVeil delivers elite, AI-powered penetration testing at unprecedented speed and scale.
Last updated: February 28, 2026
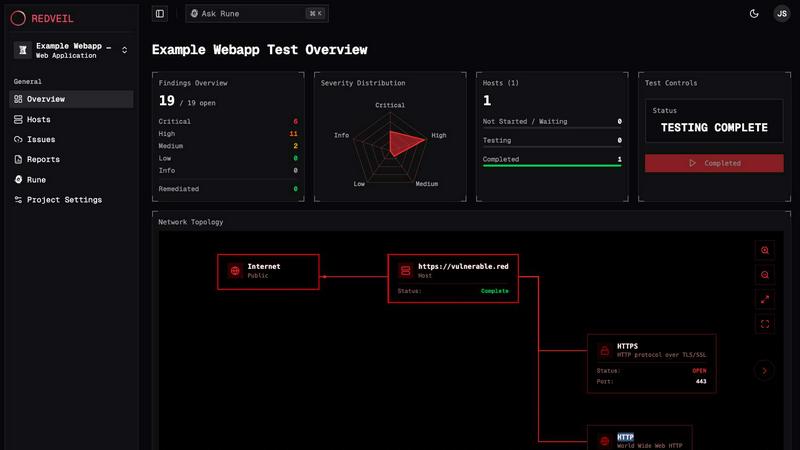
Visual Comparison
Hush Touch | Voice-to-Text for MacOS

RedVeil
Feature Comparison
Hush Touch | Voice-to-Text for MacOS
Dual-Engine Recognition
Hush Touch harnesses the power of two cutting-edge Apple dictation engines. The DictationTranscriber facilitates natural flow and punctuation, while the SFSpeechRecognizer enhances vocabulary recognition, ensuring accurate transcription of specialized terms.
Custom Vocabulary
With the ability to accommodate up to 500 unique terms, Hush Touch learns your vocabulary over time. This feature is particularly beneficial for professionals who frequently use technical jargon or industry-specific language, ensuring accurate recognition.
Smart Text Processing
Experience real-time transcription with advanced text processing capabilities. Hush Touch removes filler words, auto-corrects common errors, and formats text, including numbered lists, all executed locally to maintain speed and privacy.
Context Modes & Hands-Free Functionality
Switch effortlessly between various context modes—General, Email, Code, and Notes—tailoring the app's behavior to your specific needs. Activate hands-free dictation by using Siri commands, allowing you to dictate messages without manual intervention.
RedVeil
Autonomous AI Attack Agents
RedVeil deploys intelligent AI agents engineered to reason, exploit, and uncover multi-step attack chains like a sophisticated human adversary. These agents autonomously navigate your environment, identifying chained vulnerabilities that represent true business risk, not just isolated flaws. This delivers manual-level depth with automated speed, providing unparalleled insight into your actual security posture.
On-Demand Testing & One-Click Retesting
Eliminate the scheduling delays and scoping calls of traditional consulting. Initiate a full-scale penetration test precisely when you need it—post-deployment, pre-audit, or on a regular cadence. The platform’s one-click retesting capability allows you to validate remediation efforts instantly, enabling a continuous cycle of test, fix, and verify that aligns with modern development sprints.
Compliance-Ready Reporting Engine
Generate executive-grade, professional reports tailored for key stakeholders with a single click. RedVeil’s reporting is meticulously structured to meet the stringent requirements of major frameworks including SOC 2, ISO 27001, and PCI-DSS. Each finding includes clear evidence, contextual risk analysis, and step-by-step reproduction guidance, streamlining your audit preparation.
Guided Remediation & Expert Support (Rune)
Beyond identification, RedVeil provides guided remediation through its integrated expert support system, Rune. This feature offers clarity on complex findings, helps scope future tests, and provides actionable fix guidance in plain language. It ensures your team can effectively understand and address every vulnerability, closing the loop between discovery and resolution.
Use Cases
Hush Touch | Voice-to-Text for MacOS
Professional Communication
Draft emails and professional correspondence hands-free with Hush Touch. The app's accuracy and context-aware features make it an ideal tool for busy professionals looking to streamline their communication processes.
Note-Taking in Meetings
Capture essential notes during meetings without the distraction of typing. Hush Touch allows for natural dictation, ensuring that key points are recorded accurately without interrupting the flow of discussion.
Content Creation
Writers and content creators can utilize Hush Touch to generate ideas and content effortlessly. The app's ability to learn vocabulary enhances its utility for various writing styles and genres, making it a versatile companion.
Academic Use
Students can benefit from Hush Touch by dictating lecture notes or drafting essays. The app's precision and adaptive learning capabilities allow it to recognize academic terms and jargon, facilitating effective study habits.
RedVeil
Continuous Compliance Validation
For organizations bound by SOC 2, ISO 27001, or PCI-DSS, RedVeil provides on-demand, evidence-backed testing to validate controls continuously. Instead of an annual scramble before an audit, teams can run tests quarterly, monthly, or even post-release, ensuring they are always audit-ready with professional reports that satisfy auditor requirements instantly.
Pre-Production & Post-Deployment Security Gates
Integrate RedVeil into CI/CD pipelines or run it immediately after major deployments. This use case allows engineering teams to perform a rapid, autonomous security assessment before pushing to production or to validate that new features and code changes have not introduced critical vulnerabilities, effectively acting as a security quality gate.
Proactive Attack Surface Management
Security teams can operationalize regular penetration testing across their external perimeter and internal networks without exhausting budget or waiting for consultants. By scheduling recurring tests, they gain continuous visibility into their evolving attack surface, identifying and prioritizing new risks as they emerge in real-time.
Third-Party & M&A Due Diligence
During vendor assessments or mergers and acquisitions, RedVeil enables rapid, independent security evaluation of external assets. Quickly spin up a test against a target web application or network segment to uncover potential security liabilities, providing critical data to inform risk-based business decisions without lengthy engagement processes.
Overview
About Hush Touch | Voice-to-Text for MacOS
Hush Touch is an innovative voice-to-text application tailored specifically for macOS users, designed to transform dictation into a seamless, efficient, and private experience. By harnessing the power of dual Apple transcription engines and an advanced Apple Intelligence final pass, Hush Touch delivers remarkably accurate text output, all processed locally on your device. This feature ensures that your dictation remains private, eliminating cloud dependency and safeguarding sensitive information. With a lightweight footprint of just 5.5 MB, the app launches swiftly and integrates effortlessly into any writing workflow. Whether drafting emails, taking notes, or creating documents, Hush Touch allows users to dictate naturally, auto-inserting text after brief pauses. It's a game-changer for professionals, students, and anyone who values efficiency and privacy in their writing process.
About RedVeil
RedVeil is the definitive standard for modern, elite security validation, redefining penetration testing for the age of continuous deployment. It transcends the limitations of traditional, manual pentesting—slow, expensive, and point-in-time—by delivering the strategic reasoning of a world-class human hacker at the speed and scale of autonomous software. Designed for forward-thinking engineering and security teams who ship code daily, RedVeil operationalizes security excellence. You can spin up a comprehensive, AI-driven penetration test in minutes, not weeks, and receive a detailed, actionable, and audit-ready report within hours. This paradigm shift empowers organizations to integrate deep security assessment seamlessly into their development lifecycle, ensuring continuous protection without compromising velocity. RedVeil is for those who refuse to choose between speed and depth, offering proven, agent-driven intelligence that uncovers real, exploitable risks and complex attack paths, making proactive security an integrated advantage, not an operational bottleneck.
Frequently Asked Questions
Hush Touch | Voice-to-Text for MacOS FAQ
Is Hush Touch compatible with all MacOS versions?
Yes, Hush Touch is designed to be compatible with a range of macOS versions, ensuring that users can take advantage of its features across various devices.
How does Hush Touch ensure privacy?
Hush Touch operates entirely on-device, meaning all voice data is processed locally without the need for cloud storage or internet connectivity, ensuring maximum privacy for users.
Can I customize command phrases for sending messages?
Absolutely. Hush Touch allows users to set customizable command phrases, enabling seamless voice-activated messaging that fits your unique style.
What is the pricing structure for Hush Touch?
Hush Touch is available for a one-time purchase of $20, providing users with a lifetime license without any recurring subscription fees. This makes it an economical choice for voice-to-text solutions.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Absolutely. RedVeil is not a simple vulnerability scanner. It is an autonomous AI platform that performs genuine penetration testing by deploying agents that reason through multi-step attack chains, exploit identified vulnerabilities, and provide verified, exploitable findings with clear evidence—mirroring the methodology and depth of a skilled human penetration tester.
How many penetration tests can I do with my annual subscription?
Testing capacity is based on a transparent "Agent Ops" effort model. Your subscription tier (Perimeter, Full Coverage, Enterprise) includes an annual allocation of Agent Ops. You can use these ops to run multiple tests throughout the year, with the frequency and scope of each test determining the ops consumed. This provides predictable pricing and flexible testing cadence.
Can I use RedVeil's reports to meet my compliance requirements?
Yes. RedVeil’s reports are professionally engineered to be audit-ready for major compliance frameworks including SOC 2, ISO 27001, and PCI-DSS. They provide the detailed evidence, risk ratings, and remediation guidance that auditors require. The platform is designed specifically to streamline and substantiate your compliance efforts.
What types of testing do you offer? Is authenticated testing supported?
RedVeil currently offers comprehensive external web and network penetration testing. Authenticated testing, which assesses application functionality behind login walls, is a supported and critical capability for depth. Internal network testing is also on the roadmap, as indicated in the Full Coverage plan, ensuring expanding coverage for complex environments.
Alternatives
Hush Touch | Voice-to-Text for MacOS Alternatives
Hush Touch | Voice-to-Text for MacOS is an advanced dictation application designed specifically for macOS users. This innovative tool falls under the AI Assistants category, providing a seamless experience for anyone looking to convert speech into text offline. Users often seek alternatives to Hush Touch for various reasons, including pricing, desired features, or compatibility with different platforms. Some may also look for options that cater to specific use cases or integrate more smoothly with their existing workflows. When selecting an alternative, it's essential to consider the application's performance, privacy features, and ease of use. Users should prioritize solutions that offer reliable transcription accuracy, minimal setup, and the ability to function offline, ensuring that their dictation experience remains fluid and efficient. The right choice will ultimately depend on individual needs and preferences.
RedVeil Alternatives
RedVeil is a pioneering agentic AI platform that redefines penetration testing for the modern enterprise. It delivers autonomous, on-demand security assessments, merging elite human-level reasoning with unprecedented software speed to provide continuous, audit-ready vulnerability insights. Organizations may explore alternatives for various strategic reasons, such as budget constraints, specific compliance framework requirements, or the need for a different integration model within their existing security stack. The search often stems from a desire to balance cutting-edge capability with precise operational fit. When evaluating options, discerning teams should prioritize proven efficacy over marketing claims, scrutinizing the depth of vulnerability discovery, the sophistication of the underlying AI, and the professionalism of output. The true benchmark is a solution that seamlessly embeds elite security rigor into the continuous development lifecycle without becoming a bottleneck.
